A New Standard for Privacy
Privacy is a baseline natural desire
Privacy is an underrated luxury that most people don’t think about until it’s gone. While people chase fame, plenty of public figures have spoken about how exhausting it is to have every moment picked apart. People make mistakes, but imagine if those moments are amplified and on loop for everyone to see. Remember that time you tripped while crossing the road? The world just made a meme out of it.
However, we live in an age of surveillance. Companies compete for access to our data, what we do, what we like, and how we spend. User preferences are used for more specific ad targeting. Artificial intelligence will only accelerate the ability for external third parties to piece together information about you.
A lack of blockchain privacy is a flaw in the current design
Blockchain transactions lack privacy. While conducted pseudo-anonymously, the majority of transactions since Satoshi’s genesis block in January 2009 are publicly recorded, permanently indexed, and easily accessible to anyone with tools like Nansen or Arkham. If you momentarily expose your screen, anyone can suddenly trace what you spend, what you earn, and how you move assets.
Nonetheless, governments have been reluctant to legitimise privacy solutions; many are seen as non-compliant, with limited safeguards against misuse by bad actors operating on these rails.
However, as institutional participants enter the market, privacy becomes increasingly important; it’s not just about “having something to hide,” but rather protecting proprietary strategies while remaining compliant.
Privacy is more relevant than ever
As a result, the market has begun to develop real solutions for onchain privacy. Privacy coins were the best-performing crypto sector of 2025 by a wide margin (up 288% YoY) while Bitcoin and Ethereum largely flatlined. Zcash surged 861% before the broader privacy narrative peaked, eventually giving way to market-wide selling pressure.
Even if the cycle has cooled, the underlying infrastructure has finally matured: zero-knowledge proofs have moved from academic papers to production-grade systems, enabling private transactions that settle in seconds without sacrificing verifiability, preserving one of crypto’s core promises.
Beyond the financial aspect of privacy, much more is at stake.
In this context, Starknet is introducing STRK20, a new standard that enables any ERC20 token to be privately transferred without rebuilding infrastructure, fragmenting liquidity, or introducing compliance risks.
At the same time, strkBTC launched as a Bitcoin-backed asset that is private by default, programmable, and redeemable 1:1 for native BTC.
Different Approaches To Privacy
This section highlights four different approaches to privacy in blockchains.
1. Privacy through token transfers, which conceals the sender, receiver, and amount of a transaction between wallets.
Monero and Zcash are cases in point where
Monero uses ring signatures and stealth addresses to make every transaction private by default.
Zcash relies on zk-SNARKS to enable shielded transactions.
The limitation, however, is structural. Privacy at the token transfer layer breaks down the moment users need to interact with markets rather than simply move funds between addresses. As soon as users want to swap, lend, borrow, or participate in any protocol that depends on observable shared state, privacy becomes a constraint. Users are either forced to unshield, exposing their positions at the exact moment it matters most, or are effectively blocked from market participation entirely.
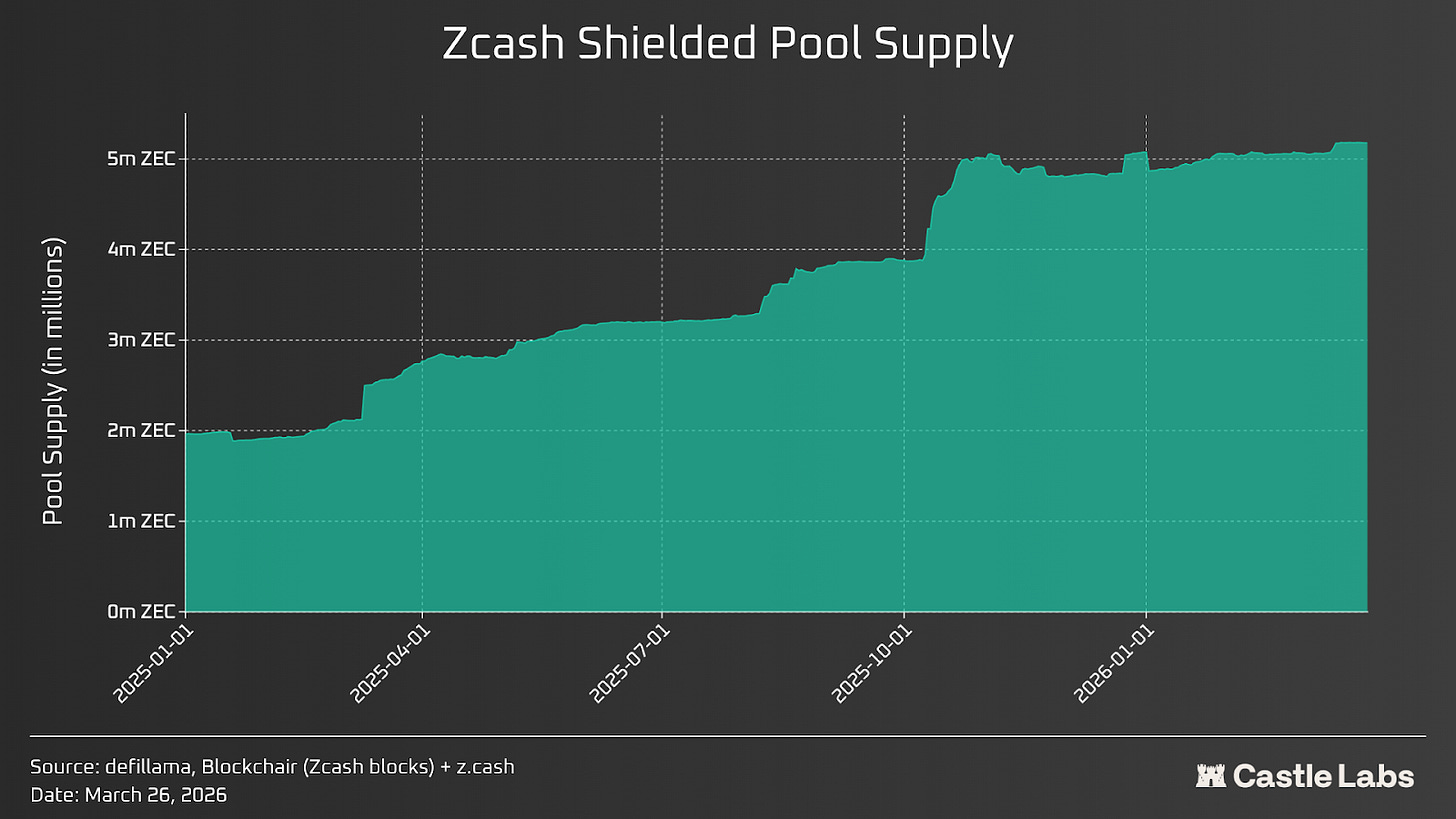
Historically, adoption of Zcash shielded pools has remained between 10% and 30% of the total supply, as users default to transparent transactions when they need composability. Even Zcash Connect, the bridge to Ethereum DeFi, requires unshielding at every protocol boundary.
More broadly, the challenge of market participation remains unresolved. These assets have largely stayed on the fringe, with limited adoption across both retail and institutional users, precisely because privacy, in its current state, comes at the cost of usability and integration.
2. Privacy through applications: building confidential applications on top of public blockchains. These systems encrypt user activity at the application layer while leaving the underlying execution environment transparent.
The tradeoff with this system is fragmentation. Each application becomes its own privacy domain, which limits interoperability. Critical data, such as price feeds, liquidation triggers, and settlement states, cannot cross application boundaries without naturally leaking information. DeFi depends on this level of shared visibility. For example, a lending protocol must track DEX prices to manage collateral risk, or a DEX must track funding rates set by spot market dynamics to effectively price its own products. Privacy in this model starts to conflict with composability.
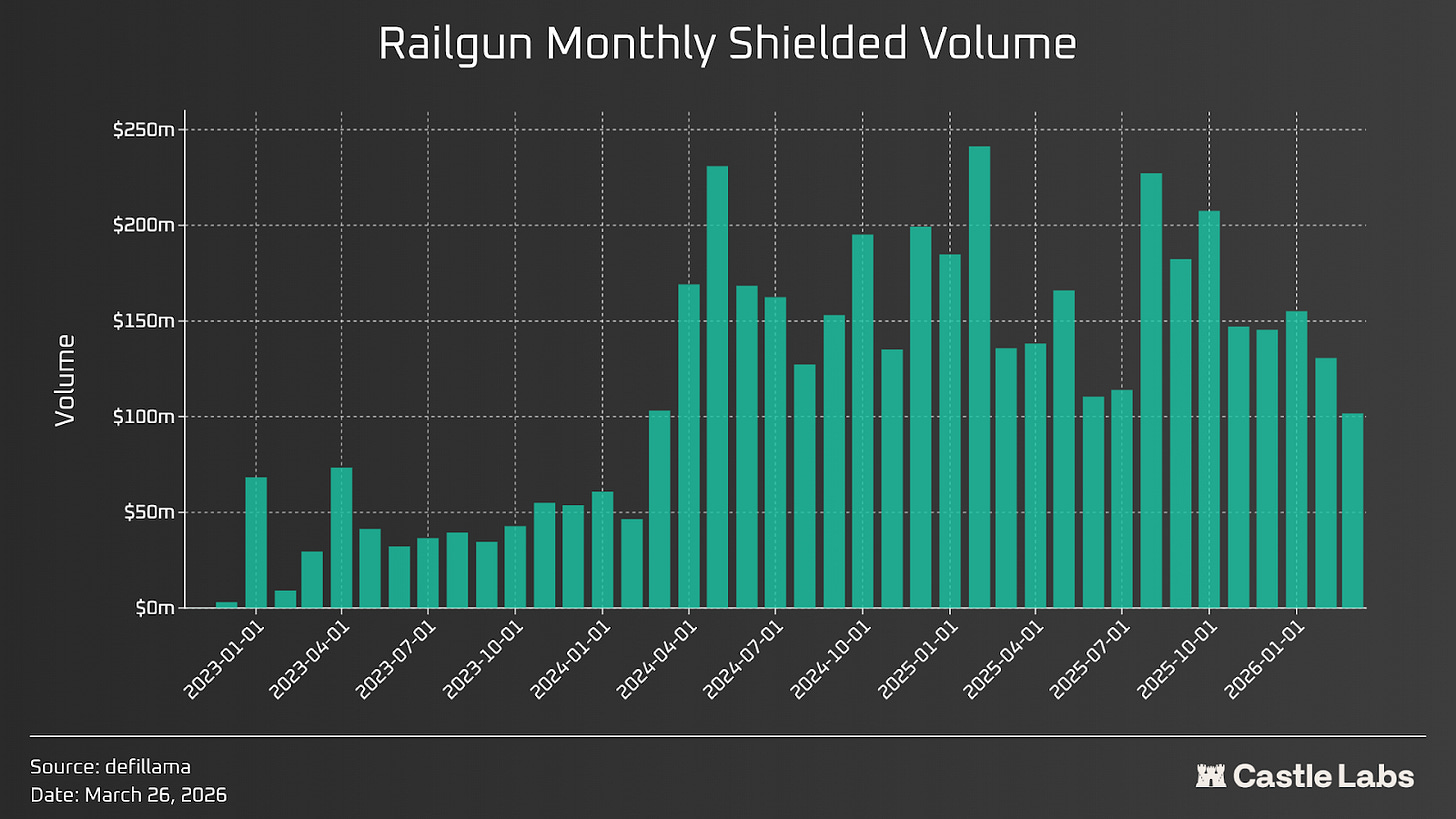
Within this category, Railgun is the most successful implementation. Backed publicly by Vitalik Buterin, Railgun processed $1.6 billion in shielded transactions in 2025 and hit $4 billion in cumulative volume. It applies zk-SNARKs at the smart contract level on Ethereum, allowing users to shield any ERC-20 token and interact with DeFi protocols from within a private balance. But Railgun remains an application sitting on top of a transparent chain. TVL bounds the anonymity set in the shielded pool (currently around $83 million), which means a sufficiently motivated chain analyst at the IRS can narrow the set of possible participants. It is the best version of app-level privacy, but it’s not bulletproof.
3. Privacy through executions: encrypting the smart contract execution itself so that neither the state nor the computation is visible to external observers.
This is Aztec’s approach, attempting to resolve the fundamental conflict between encrypted execution and usable markets. The Aztec Ignition Chain launched with 185 operators and 3,400+ sequencers.
Zama approaches the same problem from a different cryptographic direction. Rather than ZK proofs, Zama uses fully homomorphic encryption (like Octra, another recently funded protocol), computation on data that remains encrypted throughout processing, including during execution.
Its fhEVM allows developers to write confidential smart contracts in standard Solidity, where encrypted state coexists alongside public state on any EVM-compatible chain without modifying the underlying blockchain.
In theory, FHE solves the composability problem that undermines the privacy of ZK-based execution, allowing protocols to interact with each other’s encrypted state. In practice, FHE remains orders of magnitude slower than native computation, the coprocessor network is still in testnet, and no DeFi app has demonstrated that the latency is tolerable for operations like liquidations or arbitrage.
Tornado Cash struggled not because of its mechanics, but because regulators killed it. A non-custodial Ethereum mixer operating at the transfer tier without any compliance, it recorded billions in volume at its peak. On August 8, 2022, OFAC sanctioned Tornado Cash, the first time an immutable, open-source smart contract was sanctioned, and volume collapsed by nearly 85% within weeks. Those sanctions were eventually lifted after a court ruled the Treasury had overstepped its authority over open-source smart contracts.
Developer Roman Storm was convicted in August 2025 on one count of operating an unlicensed money-transmitting business, but a jury deadlocked on the more serious money laundering and sanctions charges. As of March 2026, the DOJ is pushing for an October 2026 retrial, somehow just weeks after the Treasury acknowledged in a report to Congress that mixers can serve legitimate financial privacy purposes.
The bottom line is that privacy tools without a compliance framework can be scrutinised by regulators regardless of their technical soundness. This risk would not disappear if the legal outcome is reversed, as the reputational risk of potential non-compliance is detrimental to the firm’s reputation. CertiK noted that the mere use of these coins poses significant operational risks for both platforms and users. For mainstream privacy that’s adoptable by institutions and retail alike, a compliant and scalable version is necessary.
Each of the above approaches features a major issue
Privacy through token transfers isolates users.
Privacy through applications fragments DeFi
Privacy through execution prevents trading.
A mixer that is not compliant violates the protocol regardless of its technical merit.
The only path through all four failure modes requires an entirely different architectural approach.
4. Privacy through ownership
In this approach, markets remain public, while users can remain private.
Market structure remains fully visible, including prices, liquidity, settlement, and protocol interactions. What disappears is the user layer: wallet addresses, positions, transaction history, and trading strategies. The success of Extended on Starknet suggests real demand for exactly this tradeoff: with $180 million in TVL and $156 billion in cumulative volume, Extended has become a reference in the trading sector.
Onchain analytics can show that trades occurred, but not who made them, what positions they hold, or how wallets are connected. Composability stays intact. Surveillance becomes impossible. The result is essentially Bitcoin’s permissionlessness without its privacy vacuum, and without the regulatory red flag of total opacity.
So far, achieving privacy through ownership has not been feasible, as it requires a specific infrastructure property from scratch, that is to say, the ability to verify transaction correctness without transaction visibility.
To that extent, optimistic rollups are not the ideal tech stack for privacy:
A rollup that uses fraud proofs must publish execution data for challengers to verify, and that data, in turn, is the surveillance flaw.
A rollup that uses validity proofs generated by the sequencer requires trusting the sequencer.
Enabled through ZK rollups
This is solved with ZK rollups. A ZK rollup with validity proofs generated by a decentralised prover network can verify that the cryptographic proof for every transaction is correct without needing to see the transaction itself. As such, it allows execution correctness and execution privacy to coexist.
The ZK proof infrastructure was built before privacy was a commercial priority and has been running in production for nearly a decade. Its applied result is now the STRK20 standard from StarkWare.
strkBTC, the first model for STRK20
While STRK20 is an engineering concept, strkBTC, announced at the beginning of February, is its first and most consequential application, addressing the most specific pain point in Bitcoin.
Sizing the $20B Annual Opportunity
Bitcoin processes close to half a million transactions per day. At a $100,000 BTC price, this represents more than $20 billion in annual, fully public economic activity, all recorded onchain. However, more than 2.5 million BTC, over $225 billion, sits in centralised exchange custody. Less than 0.5% of the total Bitcoin supply participates in DeFi, while Ethereum protocols routinely deploy 40% to 60% of the circulating supply into active positions. The infrastructure does not exist, and, logically, Bitcoin-adjacent activity offers no incentives.
strkBTC is a Bitcoin-backed asset issued on Starknet, redeemable one-to-one for native BTC at any time, with no algorithmic backing, secured by a federation of institutional signers operating a multisig bridge, no fractional reserve, and no synthetic exposure. Because strkBTC follows the STRK20 standard, balances are not publicly visible on Starknet, and transfers do not reveal the sender, receiver, or amount.
The STRK20 supports two standards:
In unshielded mode, strkBTC behaves like a standard ERC-20 token. Balances and transfers are public and fully verifiable by any curious regulator or fiscal authority.
In shielded mode, [strkBTC] balances and transfers are protected. Ownership and transaction details are hidden from public view, but can be selectively disclosed to specific parties upon request.
The same Bitcoin that currently generates $20 billion in annual economic activity becomes, on Starknet, an asset that can be held, transferred, lent, and traded without any of that activity appearing onchain. The 2.5 million BTC currently on exchanges for privacy reasons now has an alternative that does not require surrendering custody to, more often than not, antagonistic offshore exchanges.
Anonymous Swaps: The Litmus Test for Scalable Anonymous Blockchains
The hardest initial application is a shielded swap: a trade executed against a public AMM that does not reveal the trader, the trade size or the trade direction.
Anonymous swaps are the litmus test because they force privacy to coexist with and encompass pricing, liquidity, and execution order. Previous systems have historically failed this test.
For example, a user attempting a swap via Tornado Cash-style systems encountered a broken sequence: unshield funds from the privacy pool, execute the swap on a public DEX while fully exposed in the mempool, and then reshield the output.
Each step is a potential window that may break a private flow:
The unshielded transaction reveals that funds are leaving the privacy pool and entering a public wallet.
The swap transaction exposes the full trade to sandwich bots in the mempool.
The reshielded transaction links the post-swap balance back to the privacy pool. The net result is that the most sensitive part of the interaction, the trade itself, is the most exposed.
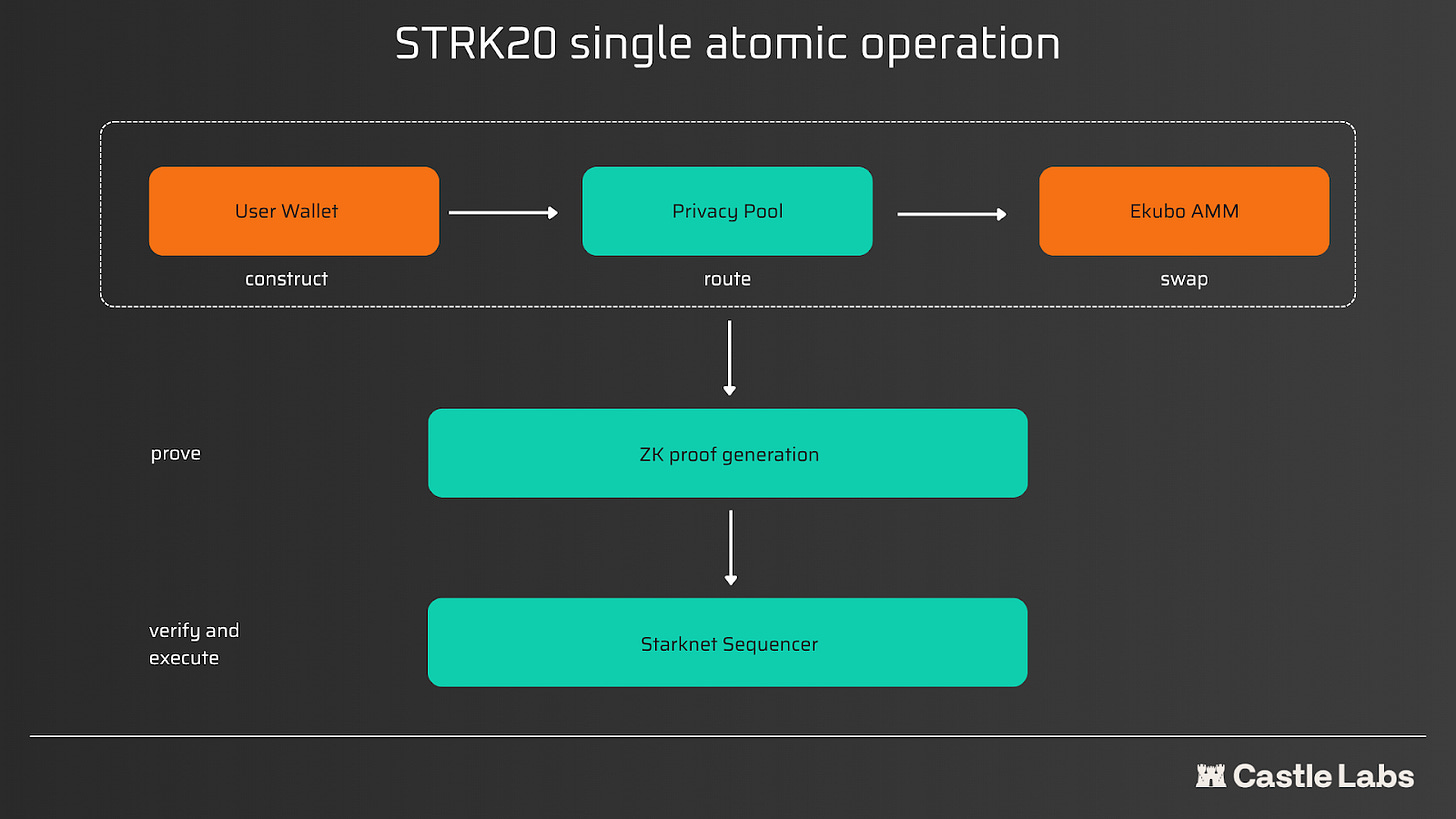
STRK20 collapses all three steps into a single atomic operation:
The user’s wallet privately constructs the swap, selecting encrypted notes from the privacy pool.
Routes it through Ekubo’s AMM.
Generates a ZK proof that the entire sequence is valid.
The Starknet sequencer verifies the proof and executes atomically.
Under this standard, there is no intermediate public state and no unshield-before-swap window for front-runners.
Trades settle at the market price visible to all participants. The AMM only sees the trade size in order to price it, which requires price discovery. What the AMM does not see is who submitted it, where the funds originated, or where they go post-execution. This now changes for traders. A sandwich bot cannot front-run a trade it cannot see in the mempool. An analytics firm cannot reconstruct a position that was never disclosed.
As an example, Ekubo provides liquidity, while shielded strkBTC and unshielded USDC interact with the same pool. There is no separate privacy DEX to bootstrap from zero liquidity. The market depth that exists on Starknet from day one is the market depth available to private users from day one.
The Five Pillars of STRK20 and the Six Problems of Privacy
Specifically, STRK20 works as follows:
When a user shields a token, the contract creates an encrypted note that does not reveal the owner or amount and hashes it into a Merkle tree onchain.
When the user spends it, he reveals a nullifier, a one-time code that proves the note is theirs and marks it as used.
A ZK proof ties it together: the network confirms the transaction is valid without learning who sent what to whom.
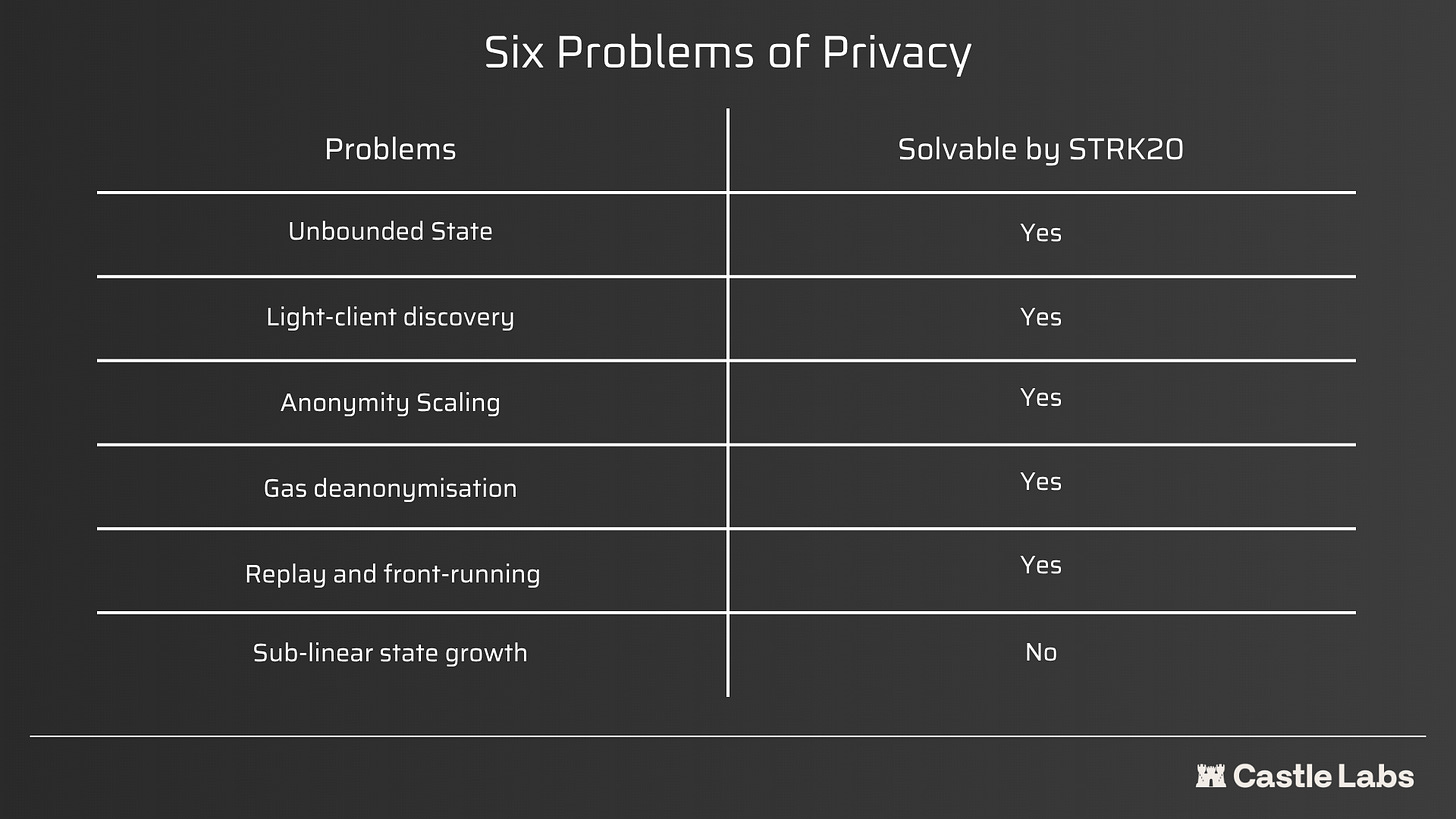
The 2024 SoK paper from Yale, George Mason, and Mysten Labs identified six open problems that are blocking blockchain privacy from scaling and, logically, from becoming mainstream.
STRK20 addresses five of those:
Unbounded state (Problem 1): A single canonical contract at the protocol level instead of emulating UTXOs inside a smart contract.
Light-client discovery (Problem 2): S-two proves in seconds, onchain encrypted channels let the wallet find incoming funds instantly without scanning the chain, the problem that killed Zcash and Monero on mobile.
Full anonymity scaling (Problem 3): A note-based model, rather than encrypted account balances, means validator work scales with transactions, not total users.
Replay and front-running (Problem 4): Note consumption plus sequencer-level verification avoids the one-transaction-per-epoch cap that cripples account-based schemes.
Gas deanonymisation (Problem 5): Paymasters allow users to pay for gas in any token via the privacy pool (no public address required).
Sub-linear state growth (Problem 6): Remains unsolved. Nullifier sets still grow linearly. This is a known tradeoff, as the current design prioritises composability and compliance, with state efficiency on the longer-term roadmap
On compliance, an important compromise as crypto becomes more regulated, is that a threshold-controlled integrity council holds encrypted viewing keys. A lawful request reconstructs one user’s history without touching the rest of the pool. This is the same structure as Swiss banking confidentiality and the same logic as GDPR data requests, with no direct access to every single piece of information regarding a user’s activities.
Conclusion
Every serious privacy attempt in crypto has failed the same way. Tornado Cash failed because OFAC had no lever to pull except obliterating the whole protocol. Zcash shielded pool adoption never broke 30% because users unshielded the moment they wanted to do anything useful. Aztec is still figuring out whether encrypted execution and usable markets can coexist. The pattern is consistent enough to warrant a serious inquiry into how crypto can remain both compliant and private, without a catastrophic downside or the protocol being deserted.
STRK20 is a genuinely different architecture. Markets stay public, users stay private, and a compliance mechanism gives regulators something to work with short of sanctioning the whole ecosystem. Whether that satisfies OFAC in practice is a question regulators will ultimately answer, but the architecture at least gives them a lever that didn’t exist before. The institutional change of heart shows that DeFi is no longer a niche. Allocators are no longer individuals in search of high-risk, high-reward investments.
The $225 billion in BTC sitting on centralised exchanges is there because the infrastructure to hold it privately, use it in DeFi, and remain redeemable one-to-one for native BTC did not exist. Less than 0.5% of the Bitcoin supply participates in DeFi, while Ethereum protocols routinely deploy 40-60% of the circulating supply. That gap remains unresolved, and previous attempts have not worked.
As we enter a different cycle, defined by an overwhelming appetite from institutions and, paradoxically, a fearful retail, compliant privacy might be the last bastion for individuals looking to preserve their sovereignty.
written by @TradFiHater ✍️
Every week for the last 3 years, we have shared our research for free, directly in your email. Not a subscriber yet? Let’s fix it:
If you are more of a Telegram person, you can read all of our research without the noise on our TG channel:
Disclaimer: This article was produced in collaboration with Starknet. Castle Labs applies the same standard to sponsored content as in our independent research. We strive to be accurate, unbiased and educational. Commissioned partnerships provide resourcing and distribution, not editorial control.